Advanced Apple Debugging & Reverse Engineering, Chapter 31
Por um escritor misterioso
Last updated 13 abril 2025

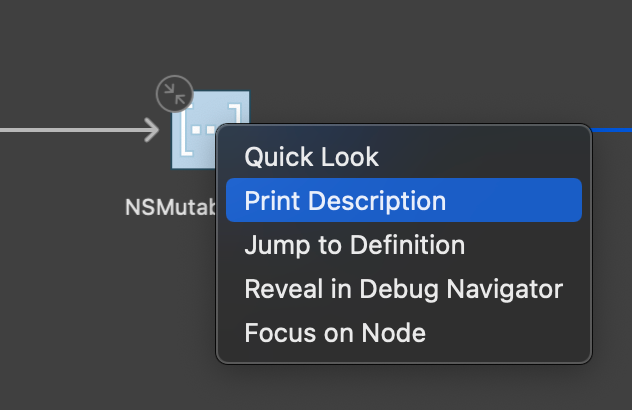
In this chapter, you'll use DTrace to hook objc_msgSend's entry probe and pull out the class name along with the Objective-C selector for that class. By the end of this chapter, you'll have LLDB generating a DTrace script which only generates tracing info for code implemented within the main executable that calls objc_msgSend.

2022-2023 College Catalog by Honolulu Community College - Issuu

Advanced Apple Debugging & Reverse Engineering, Chapter 11: Assembly Register Calling Convention
Kodeco Learn iOS, Android & Flutter

Practical Reverse Engineering: x86, x64, ARM, Windows Kernel, Reversing Tools, and Obfuscation: 9781118787311: Computer Science Books @

Reverse Engineering: Binary Security, by Totally_Not_A_Haxxer
IOS Reverse Engineering - Configuring LLDB
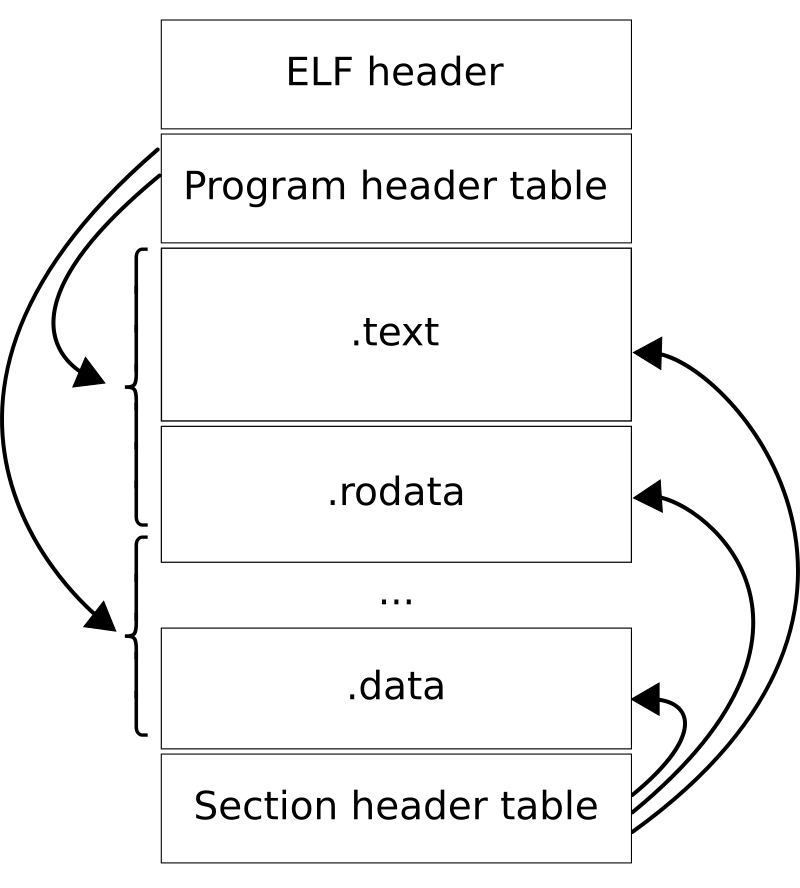
Executable and Linkable Format - Wikipedia

Advanced Apple Debugging & Reverse Engineering, Chapter 1: Getting Started
How to Reverse Engineer an iOS App, by Zafar Ivaev

LLDB's Runtime Manipulation: A Guide to Advance Debugging and Optimization

Advanced Apple Debugging & Reverse Engineering, Chapter 1: Getting Started
Recomendado para você
-
Fer99913 abril 2025
-
 como canjear en rbx gum|Búsqueda de TikTok13 abril 2025
como canjear en rbx gum|Búsqueda de TikTok13 abril 2025 -
 New rbx.gum promocode june 6,202213 abril 2025
New rbx.gum promocode june 6,202213 abril 2025 -
 Ways On How To Get Free robux from rbx .gum13 abril 2025
Ways On How To Get Free robux from rbx .gum13 abril 2025 -
Discuss Everything About Bubble Gum Simulator Wiki13 abril 2025
-
Cheeks Joy Blush Face Roblox Item - Rolimon's13 abril 2025
-
robloxapi · GitHub Topics · GitHub13 abril 2025
-
 trading random roblox acc (no rh or am stuff sry;c) : r/CrossTrading_inRoblox13 abril 2025
trading random roblox acc (no rh or am stuff sry;c) : r/CrossTrading_inRoblox13 abril 2025 -
 Seed Junky Home13 abril 2025
Seed Junky Home13 abril 2025 -
![ALL New] RBX.GUM PROMO CODE (March 2022) Latest & Still Working Codes For RBX.GUM Free Robux?](https://i.ytimg.com/vi/lC7J9zRppjU/maxresdefault.jpg?sqp=-oaymwEmCIAKENAF8quKqQMa8AEB-AH-CYAC0AWKAgwIABABGEEgPSh_MA8=&rs=AOn4CLB8yR5aU--8FlwvrEEfO6BdjDaafQ) ALL New] RBX.GUM PROMO CODE (March 2022) Latest & Still Working Codes For RBX.GUM Free Robux?13 abril 2025
ALL New] RBX.GUM PROMO CODE (March 2022) Latest & Still Working Codes For RBX.GUM Free Robux?13 abril 2025
você pode gostar
-
 Tumbling Class - ISG Gymnastics13 abril 2025
Tumbling Class - ISG Gymnastics13 abril 2025 -
Jurassic Dinosaur: Dino Game – Apps no Google Play13 abril 2025
-
 Alya on X: Classroom of the Elite: Y2V10 Arisu Sakayanagi 📱 #you_zitsu #よう実 / X13 abril 2025
Alya on X: Classroom of the Elite: Y2V10 Arisu Sakayanagi 📱 #you_zitsu #よう実 / X13 abril 2025 -
 The Mandalorian (TV Series 2019– ) - Episode list - IMDb13 abril 2025
The Mandalorian (TV Series 2019– ) - Episode list - IMDb13 abril 2025 -
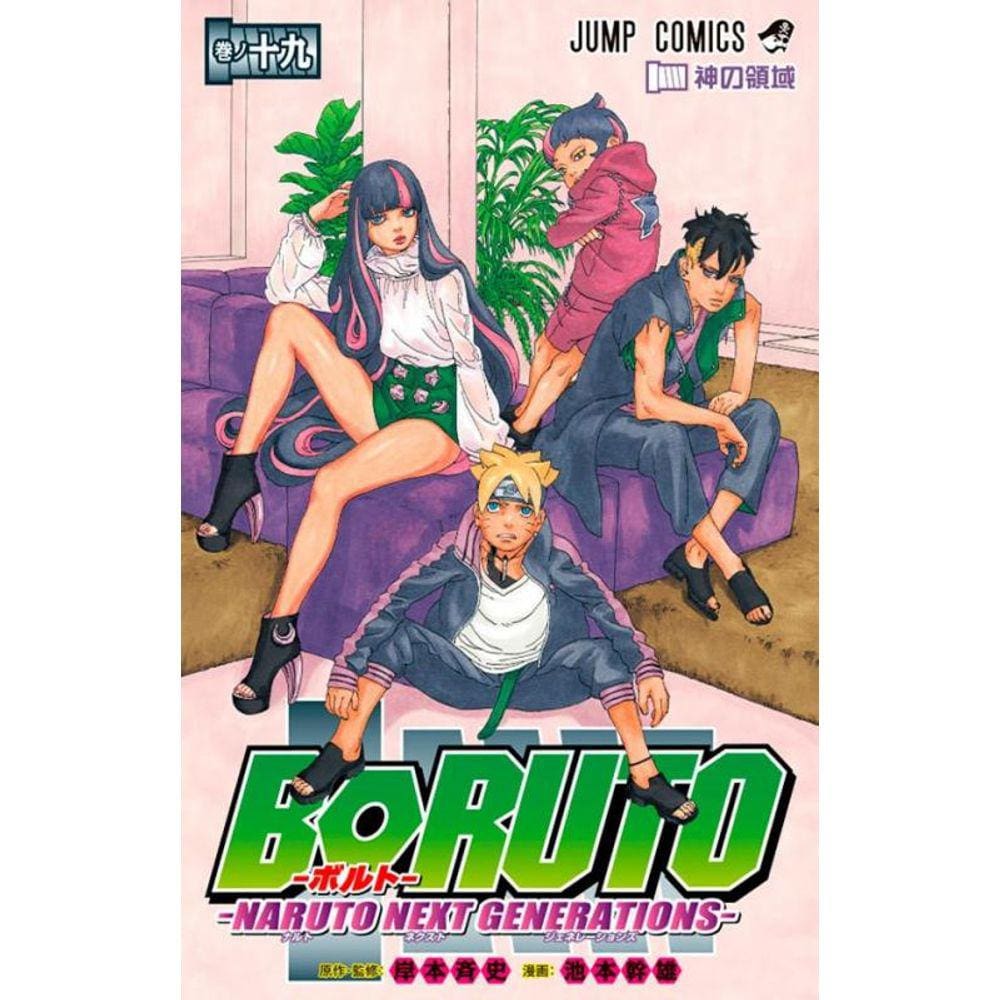 Boruto naruto next generations dublado13 abril 2025
Boruto naruto next generations dublado13 abril 2025 -
 Hebrew Slang Words and Phrases You Should Know13 abril 2025
Hebrew Slang Words and Phrases You Should Know13 abril 2025 -
 Toby (AEG), Thomas the Tank Engine Wikia13 abril 2025
Toby (AEG), Thomas the Tank Engine Wikia13 abril 2025 -
Cool Games FPS Online Gun 3D - Apps on Google Play13 abril 2025
-
 Pokemon Trainer Skin - Skin De Red Pokemon - 317x453 PNG Download13 abril 2025
Pokemon Trainer Skin - Skin De Red Pokemon - 317x453 PNG Download13 abril 2025 -
 Extended partnership Team Jumbo-Visma - CloseTheGap - Reinventing bike parts13 abril 2025
Extended partnership Team Jumbo-Visma - CloseTheGap - Reinventing bike parts13 abril 2025

